Networking & Cloud Computing
epub |eng | | Author:Roberto Di Pietro & Simone Raponi & Maurantonio Caprolu & Stefano Cresci
Gradient Hiding A large family of adversarial attacks exploits the known characteristics of the attacked model. Among the most important of such characteristics is the gradient of deep neural network ...
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | 2020-12-11 | Author:Davide Bedin
Figure 6.1 â Twilio output binding added to the Shipping service In Figure. 6.1, you can see the evolution of the shipping-service Dapr service: an output resource binding of the ...
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | 2020-12-02 | Author:Iain Anderson
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | 1998-09-30 | Author:Grady Booch & James Rumbaugh & Ivar Jacobson [Booch, Grady & Rumbaugh, James & Jacobson, Ivar]
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | | Author:Ying-Jun Angela Zhang & Congmin Fan & Xiaojun Yuan
34. M. Medard, âThe effect upon channel capacity in wireless communications of perfect and imperfect knowledge of the channel,â IEEE Transactions on Information Theory, vol. 46, no. 3, pp. 933â946, ...
( Category:
Enterprise Data Computing
February 23,2021 )
epub |eng | | Author:Dr. Hedaya Mahmood Alasooly
h) Sending Ether & Events Now let's write a function that accepts Ether. To demonstrate this, I'll create an ico-like contract with a buyToken() function. This will allow an account ...
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | 2000-01-02 | Author:Jim Highsmith & Linda Luu & David Robinson [Jim Highsmith & Linda Luu & David Robinson]
Figure 6-4 Example of product within LVT (measures and targets omitted for simplicity). Figure 6-5 Example of a consumer platform and product within LVT (measures and targets omitted for simplicity). ...
( Category:
Industries
February 23,2021 )
epub |eng | 2020-12-22 | Author:A, Tanveer [A, Tanveer]
Output : #columns identified as features are as below: #['Cruise_line','Age','Tonnage','passengers','length','cabins','passenger_density'] #to work on the features, spark MLlib expects every value to be in numeric form #feature 'Cruise_line is string datatype ...
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | | Author:Thimira Amaratunga
Once we have the trained model, we will define the parameters for the fine-tuning, as well as resetting our data generators so that we can reuse them. We are setting ...
( Category:
Networking & Cloud Computing
February 23,2021 )
epub |eng | | Author:Frontend Masters [Frontend Masters]
( Category:
Networking & Cloud Computing
February 23,2021 )
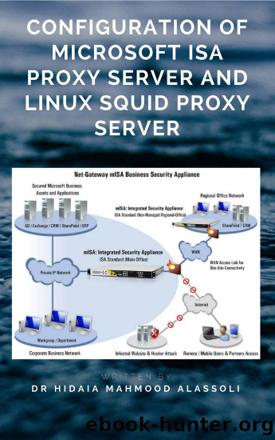
epub |eng | | Author:Dr. Hidaia Mahmood Alassouli [Alassouli, Hidaia Mahmood]
With my configuration, I set IP address: 10.12.1.149 and the Port:8080 The following procedure made the following changes in the squid config file /etc/squid/squid.conf: http_port 10.12.1.149:8080 icp_port 3130 3. 3. ...
( Category:
Cloud Computing
February 22,2021 )
epub |eng | 2021-01-30 | Author:Falode, Elijah [Falode, Elijah]
- You can pin any of the data visualizations to any of the dashboard you like. - Because itâs a new report, you have to save the visualization before you ...
( Category:
Networking & Cloud Computing
February 22,2021 )
epub |eng | 2021-01-29 | Author:Larry L. Peterson & Bruce S. Davie [Peterson, Larry L. & Davie, Bruce S.]
( Category:
Networking & Cloud Computing
February 22,2021 )
epub |eng | | Author:Jenkins NS
( Category:
Networking & Cloud Computing
February 22,2021 )
epub |eng | | Author:Unknown
( Category:
Engineering
February 22,2021 )
Categories
Popular ebooks
The Mikado Method by Ola Ellnestam Daniel Brolund(22542)Kotlin in Action by Dmitry Jemerov(19348)
Grails in Action by Glen Smith Peter Ledbrook(16799)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(14283)
Configuring Windows Server Hybrid Advanced Services Exam Ref AZ-801 by Chris Gill(7520)
Azure Containers Explained by Wesley Haakman & Richard Hooper(7514)
Running Windows Containers on AWS by Marcio Morales(7066)
Microsoft 365 Identity and Services Exam Guide MS-100 by Aaron Guilmette(5451)
Microsoft Cybersecurity Architect Exam Ref SC-100 by Dwayne Natwick(5289)
Combating Crime on the Dark Web by Nearchos Nearchou(5043)
The Ruby Workshop by Akshat Paul Peter Philips Dániel Szabó and Cheyne Wallace(4720)
Management Strategies for the Cloud Revolution: How Cloud Computing Is Transforming Business and Why You Can't Afford to Be Left Behind by Charles Babcock(4563)
Python for Security and Networking - Third Edition by José Manuel Ortega(4295)
The Age of Surveillance Capitalism by Shoshana Zuboff(4274)
Learn Windows PowerShell in a Month of Lunches by Don Jones(4192)
Learn Wireshark by Lisa Bock(4192)
Ember.js in Action by Joachim Haagen Skeie(4072)
The Ultimate Docker Container Book by Schenker Gabriel N.;(3938)
DevSecOps in Practice with VMware Tanzu by Parth Pandit & Robert Hardt(3626)
Windows Ransomware Detection and Protection by Marius Sandbu(3599)