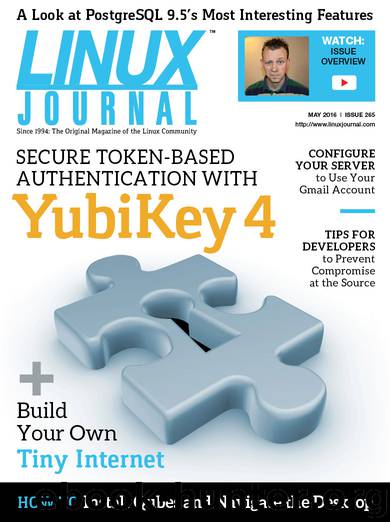
Linux Journal May 2016 by Linux Journal
Author:Linux Journal
Language: eng
Format: mobi, epub
Tags: Privacy, Chrome, Humble Bundle, Features, Bitcoin, Desktop, E-mail, Token-Based, Compromise, Android, Tiny Internet, Configure, Qubes, Glass, Amazon, 4, 9.5, Configuration, Account, Installation, Server, Epichrome, Install, YubiKey, New Math, Security, Purse.IO, PostgreSQL, Secure, Screen Protector, Navigate, KVM, Authentication, Snapchat, Casper, Linux, Gmail, Cloud, Developer
Publisher: Belltown Media
Published: 2016-04-29T07:00:00+00:00
■ Never store private keys on a system that does not have full-disk encryption.
■ Avoid creating passwordless private keys unless you understand the implications of doing so, and have another protection in place to prevent their abuse, such as encrypting the key with a key stored on a separate hardware token.
■ Keep a log of which keys you have in use where, so that if a key is compromised, you can ensure that it is revoked and replaced with a new key.
■ Use a different key on each of your machine. If one of your keys is compromised, once it is used, you know from which key it was which of your machines is in question. If all machines use the same key, you likely will have no idea where the compromise came from. Having multiple keys also is helpful when you are having someone else revoke a key for you. If I find that my laptop’s key may be compromised, but I’m away at a conference, I can make a couple phone calls to get that key revoked in the two or three places where it could cause the most damage. Then, when I get home, I can log in via my desktop (which has its own key) to place a new public key for my laptop in the appropriate places.
Download
This site does not store any files on its server. We only index and link to content provided by other sites. Please contact the content providers to delete copyright contents if any and email us, we'll remove relevant links or contents immediately.
The Mikado Method by Ola Ellnestam Daniel Brolund(25294)
Hello! Python by Anthony Briggs(24339)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(23433)
Kotlin in Action by Dmitry Jemerov(22512)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(21976)
Dependency Injection in .NET by Mark Seemann(21847)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(20711)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(19523)
Grails in Action by Glen Smith Peter Ledbrook(18607)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17034)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15843)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(13690)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(11857)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11151)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10621)
Hit Refresh by Satya Nadella(9202)
The Kubernetes Operator Framework Book by Michael Dame(8570)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8407)
Robo-Advisor with Python by Aki Ranin(8361)
