Hackers Heroes of the Computer Revolution (25th Anniversary Edition) by Hackers Heroes of the Computer Revolution (25th Anniversary Edition)
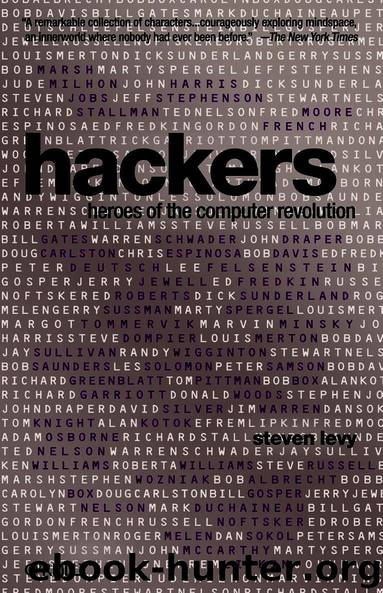
Author:Hackers Heroes of the Computer Revolution (25th Anniversary Edition) [Edition), ]
Language: eng
Format: epub
Publisher: ePub Bud (www.epubbud.com)
Published: 2011-09-26T16:00:00+00:00
Chapter 11
board for a few months. He later described the difference between the two groups: “Homebrew was a place where people came
together mysteriously, twice a month. It never was an organization. But SCCS was more organized. Those guys had megalomania. The politics were terrible, and ruined it.” Somehow, the particulars never became clear, a lot of money was misplaced in the buying scheme. The editor they hired to run the slick magazine felt justified in dropping the publication’s relationship with the club and going off on his own with the magazine (still publishing as Interface Age); a lawsuit resulted. The board meetings became incredibly tempestuous, and the bad feelings spread to the general membership meetings. Eventually the club faded away. Though Lee’s plans were no less ambitious than those of the leaders of SCCS, he realized that this war must not be waged in a bureaucratic, follow-the-leader fashion. He was perfectly happy dealing with an army of Bob Marshes and Tom Pittmans, some changing the world by dint of useful products manufactured in the spirit of hackerism and others just going their way, being hackers. The eventual goal would be a mass distribution of the wonderment that Lee Felsenstein had experienced in his basement monastery. An environment conducive to the Hands-On Imperative. As Lee told a conference of the Institute of Electrical and Electronic Engineers in 1975, “The industrial approach is grim and doesn’t work: the design motto is ‘Design by Geniuses for Use by Idiots,’
and the watchword for dealing with the untrained and unwashed public is KEEP THEIR HANDS OFF! . . . The convivial approach I suggest would rely on the user’s ability to learn about and gain some control over the tool. The user will have to spend some amount of time probing around inside the equipment, and we will have to make this possible and not fatal to either the equipment or the person.”
The piece of equipment to which Felsenstein referred was his Tom Swift Terminal, which still had not been built in 1975. But it was getting close. Bob Marsh, eager to expand the scope of his booming Processor Technology company, offered Lee a deal he couldn’t refuse. “I’ll pay you to design the video portion of the Tom Swift Terminal,” he told him. That sounded all right to Lee, who had been doing work in documentation and schematics for Processor Technology all along. Bob Marsh, in the company’s first year of business, was adhering to the Hacker Ethic. The company Tiny BASIC
243
distributed schematics and source code for software, free or at nominal cost. (In partial reaction to MIT’s high-priced BASIC, Processor Technology would develop its own and sell it, along with source code, for five dollars.) For a time, the company had a socialistic salary structure of $800 a month for all employees.
“We didn’t pay attention to profits or management of almost any kind.”
Lee was not an employee, choosing to work on a contract basis.
“I’d quote them a price,” Lee later recalled, and “they had to get the price up by a factor of ten, since I was such a small-time thinker.
Download
This site does not store any files on its server. We only index and link to content provided by other sites. Please contact the content providers to delete copyright contents if any and email us, we'll remove relevant links or contents immediately.
| Blogging & Blogs | eBay |
| E-Commerce | Hacking |
| Online Searching | Podcasts & Webcasts |
| Search Engine Optimization | Social Media |
| Social Media for Business | Web Browsers |
| Web Marketing |
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(24440)
Kotlin in Action by Dmitry Jemerov(23531)
Grails in Action by Glen Smith Peter Ledbrook(19337)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(16362)
Ember.js in Action by Joachim Haagen Skeie(5881)
WordPress Plugin Development Cookbook by Yannick Lefebvre(4502)
Mastering Azure Security by Mustafa Toroman and Tom Janetscheck(3607)
The Innovators: How a Group of Hackers, Geniuses, and Geeks Created the Digital Revolution by Walter Isaacson(3532)
Learning React: Functional Web Development with React and Redux by Banks Alex & Porcello Eve(3218)
A Blueprint for Production-Ready Web Applications: Leverage industry best practices to create complete web apps with Python, TypeScript, and AWS by Dr. Philip Jones(3162)
Mastering Bitcoin: Programming the Open Blockchain by Andreas M. Antonopoulos(3109)
The Art Of Deception by Kevin Mitnick(2857)
Drugs Unlimited by Mike Power(2651)
Hands-On Cybersecurity with Blockchain by Rajneesh Gupta(2494)
Kali Linux - An Ethical Hacker's Cookbook: End-to-end penetration testing solutions by Sharma Himanshu(2441)
Writing for the Web: Creating Compelling Web Content Using Words, Pictures and Sound (Eva Spring's Library) by Lynda Felder(2380)
SEO 2018: Learn search engine optimization with smart internet marketing strategies by Adam Clarke(2293)
JavaScript by Example by S Dani Akash(2259)
DarkMarket by Misha Glenny(2245)
