Computers & Technology
epub |eng | 2013-09-04 | Author:Alice E. Marwick
Learning a Neoliberal Ideal Both Crush It! and The 4-Hour Work Week are instruction manuals for surviving without an economic safety net. Ferriss and Vaynerchuk assume that the changes that ...
( Category:
Social Sciences
September 4,2017 )
epub |eng | 2011-10-03 | Author:Christopher Golden [Golden, Christopher]
Three hours later they were on a boat racing north on the Nile, headed for Port Said in hopes of finding a ship’s captain willing to run them northwest across ...
( Category:
Science Fiction
September 4,2017 )
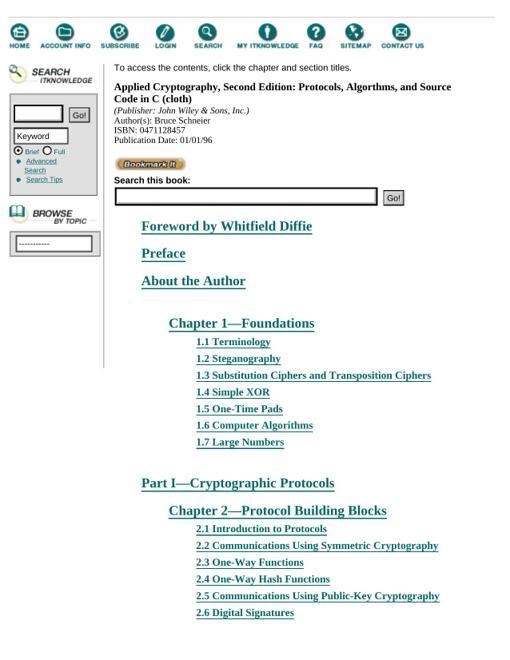
epub, azw3, pdf |eng | 2017-05-22 | Author:Bruce Schneier
Designing a Block Cipher It is easy to design a block cipher. If you think of a 64-bit block cipher as a permutation of the 64-bit numbers, it is clear ...
( Category:
Security & Encryption
September 4,2017 )
epub |eng | 2011-07-28 | Author:Kevin D. Mitnick
Chapter 11 Combining Technology and Social Engineering A social engineer lives by his ability to manipulate people into doing things that help him achieve his goal, but success often also ...
( Category:
Networking & Cloud Computing
September 4,2017 )
epub, mobi |eng | 2010-09-28 | Author:Michael Ligh & Steven Adair & Blake Hartstein & Matthew Richard
HANDLE hDupHandle; BOOL bStatus = FALSE; HANDLE hProc = OpenProcess(PROCESS_DUP_HANDLE, FALSE, dwPid); if (hProc != NULL) { if (DuplicateHandle(hProc, (HANDLE)dwHval, GetCurrentProcess(), &hDupHandle, 0, FALSE, DUPLICATE_SAME_ACCESS|DUPLICATE_CLOSE_SOURCE)) { if (CloseHandle(hDupHandle)) { bStatus ...
( Category:
Security & Encryption
September 4,2017 )
epub, pdf |eng | 2014-02-17 | Author:Adam Shostack
Social Security Numbers and Other National Identity Numbers This section reviews risks associated with the United States social security number (SSN). Over the last five to ten years, the use ...
( Category:
Security & Encryption
September 4,2017 )
epub, mobi |eng | 2014-11-03 | Author:Niels Ferguson & Bruce Schneier & Tadayoshi Kohno
The lemma is a statement of fact. The proof argues why the lemma is true. The little square box signals the end of the proof. Mathematicians love to use lots ...
( Category:
Security & Encryption
September 4,2017 )
epub |eng | 2014-07-01 | Author:Michael Hale Ligh & Andrew Case & Jamie Levy & AAron Walters
Figure 14-4: WinLister on a live machine shows the IE window properties The next image in Figure 14-5 shows a similar situation, but this time the IE process is in ...
( Category:
Security & Encryption
September 4,2017 )
epub, mobi |eng | | Author:2014
The next time you need that component, you can open that collection from the Components window and drop it directly into a model. Another way to save components to a ...
( Category:
Arts & Photography
September 3,2017 )
epub |eng | | Author:2013
And we define the query that joins these two queries.(def census-joined (<- [?name ?pop100 ?hu100 ?families ?white ?black ?indian ?asian ?hawaiian ?other ?multiple] (family-data ?geoid _ _ ?name ?pop100 ?hu100 ...
( Category:
Web Development & Design
September 3,2017 )
epub |eng | 2012-09-03 | Author:Rob Sheppard
Deciding Whether the Sky Is Worth the Effort Sky can be a very important part of your landscape photography. But sky is not always the best thing for the photo. ...
( Category:
Photography & Video
September 3,2017 )
epub |eng | 2008-01-02 | Author:Stefan Wintermeyer & Stephen Bosch [Wintermeyer, Stefan & Bosch, Stephen]
( Category:
Operating Systems
September 3,2017 )
epub |eng | 2009-02-09 | Author:William von Hagen & Brian K. Jones [Hagen, William von & Jones, Brian K.]
Figure 5-5. Specifying restore options and completion behavior Figure 5-6. Restoring the partition image Summary Creating partition image files of customized, optimized, and fine-tuned desktop and server partitions provides a ...
( Category:
Computers & Technology
September 3,2017 )
mobi, epub |eng | | Author:2014
How to do it… Perform the following steps to install the Twitter4J library as a module: Create the OpenShift application created in the Creating and deploying Java EE 6 applications ...
( Category:
Programming
September 3,2017 )
epub |eng | | Author:Don Syme, Adam Granicz & Antonio Cisternino
( Category:
Programming
September 3,2017 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(28998)The Mikado Method by Ola Ellnestam Daniel Brolund(26291)
Hello! Python by Anthony Briggs(25216)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(24446)
Kotlin in Action by Dmitry Jemerov(23536)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(22880)
Dependency Injection in .NET by Mark Seemann(22667)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(21431)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(20273)
Grails in Action by Glen Smith Peter Ledbrook(19343)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17056)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(16366)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(14077)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(12255)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11533)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10644)
Hit Refresh by Satya Nadella(9221)
The Kubernetes Operator Framework Book by Michael Dame(8579)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8432)
Robo-Advisor with Python by Aki Ranin(8376)