Computers & Technology
mobi |eng | 2009-02-09 | Author:Neal Stephenson
THE ORAL TRADITION Unix is hard to learn. The process of learning it is one of multiple small epiphanies. Typically you are just on the verge of inventing some necessary ...
( Category:
Operating Systems
November 4,2017 )
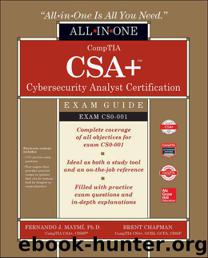
azw3 |eng | 2017-09-01 | Author:Maymi, Fernando & Chapman, Brent [Maymi, Fernando]
Forensic Duplicators Forensic duplicators are systems that copy data from a source to a destination while ensuring that not even a single bit gets altered in the process. What sets ...
( Category:
Security & Encryption
November 4,2017 )
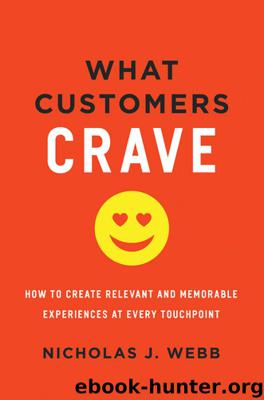
epub |eng | 2017-11-04 | Author:Nicholas J. Webb
If you follow the steps in my pre-touch plan, you not only won’t boil in the changing water temperatures of the fast-paced world but you’ll be able to use the ...
( Category:
Marketing & Sales
November 4,2017 )
epub |eng | | Author:Daniel Bartholomew
NTILE The syntax for the NTILE function is: NTILE (<ntile_expression>) OVER ( [ <partition_definition> ] [ <order_definition> ] ) This function returns an integer indicating the group a certain row ...
( Category:
Computers & Technology
November 4,2017 )
mobi |eng | 2011-09-12 | Author:The Hundred Days
Chapter Six At Durazzo they stood out to sea, leaving the blaze on their larboard quarter and sailing across an uneventful sea with a fine topgallant breeze. But two days ...
( Category:
Arts & Photography
November 4,2017 )
azw3, epub, mobi |eng | 2016-06-25 | Author:Neil, Nathan [Neil, Nathan]
Command uptime Result System will display the uptime and load average data CLI Display [tidus@centos:~]$ uptime Next we can see what processes are using the most memory on our system ...
( Category:
Operating Systems
November 3,2017 )
epub, azw3 |eng | 2017-10-09 | Author:Martin Brinkmann [Brinkmann, Martin]
Automatic learning enables the collection of speech and handwriting patterns, typing history, contacts, and recent calendar information. It is required for the use of Cortana. Some of this collected information ...
( Category:
Operating Systems
November 3,2017 )
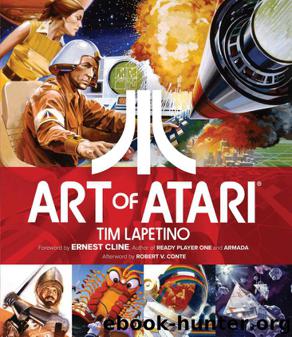
azw3 |eng | 2016-10-25 | Author:Tim Lapetino [Lapetino, Tim]
( Category:
Pop Culture
November 3,2017 )
mobi, epub, pdf |eng | 2011-06-13 | Author:user
“I had hoped that by now you would have grown tired of that wretched beard. All that hair makes you look like Robert.” His sister had put aside her mourning ...
( Category:
Web Development & Design
November 3,2017 )
epub |eng | 2013-09-30 | Author:James Barrat [Barrat, James]
Chapter Eleven A Hard Takeoff Day by day, however, the machines are gaining ground upon us; day by day we are becoming more subservient to them; more men are daily ...
( Category:
Computer Science
November 3,2017 )
mobi, epub, azw3 |eng | 2017-01-31 | Author:Igor Vishnevskiy
EXAMPLE 7.11.1 Python: array = [123, [2, 4, 6, 2, 8], "testString", {"key" : "value", "key" : "value"}, ("testStringTwo", 123)] In the above example, the first element of my array ...
( Category:
Computers & Technology
November 3,2017 )
epub, pdf |eng | 2014-12-01 | Author:Jez Humble, Joanne Molesky & Barry O'Reilly
Gojko Adzic presents a technique called impact mapping to break down high-level business goals at the program level into testable hypotheses. Adzic describes an impact map as “a visualization of ...
( Category:
Management & Leadership
November 3,2017 )
epub, mobi, azw3, pdf |eng | 2015-11-02 | Author:Rod Stephens
Because the two value variables refer to different copies of the same data, changing one doesn't change the other. For example, if you execute the statement dan.Name = "Dan", then ...
( Category:
Computers & Technology
November 3,2017 )
epub, mobi |eng | | Author:2016
Given such input, the function wraps some other complex functions. It creates n-iterations, training a model of the n-cross-validation in-samples, testing the results, and storing scores derived at each iteration ...
( Category:
Programming Languages
November 3,2017 )
azw3 |eng | 2017-10-25 | Author:Lallan, Elaiya Iswera [Lallan, Elaiya Iswera]
## Scan UDP port 53 nmap -p U:53 192.168.1.1 ## Scan two ports ## nmap -p 80,443 192.168.1.1 ## Scan port ranges ## nmap -p 80-200 192.168.1.1 ## Combine all ...
( Category:
Computers & Technology
November 2,2017 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(28998)The Mikado Method by Ola Ellnestam Daniel Brolund(26291)
Hello! Python by Anthony Briggs(25216)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(24446)
Kotlin in Action by Dmitry Jemerov(23536)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(22880)
Dependency Injection in .NET by Mark Seemann(22667)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(21431)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(20273)
Grails in Action by Glen Smith Peter Ledbrook(19343)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17056)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(16366)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(14077)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(12255)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11533)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10643)
Hit Refresh by Satya Nadella(9220)
The Kubernetes Operator Framework Book by Michael Dame(8579)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8432)
Robo-Advisor with Python by Aki Ranin(8376)