Computers & Technology
epub |eng | 2019-06-14 | Author:Walker, Brian [Walker, Brian]
Chapter 5: Initiating Breach Protocol So, let’s say the worst case scenario happens. You wake up one day preparing for work but your phone cannot stop ringing. Notifications keep dropping ...
( Category:
Cryptography
August 19,2019 )
epub |eng | 2017-03-21 | Author:Thompsons, Josh [Thompsons, Josh]
As I said earlier, Python works cross-platform and you can install it on any of these platforms: Windows CE OS/2 DOS VMS/OpenVMS Psion VxWorks PalmOS UNIX systems (Solaris, Linux, FreeBSD, ...
( Category:
Mainframes & Minicomputers
August 19,2019 )
epub |eng | 2019-08-11 | Author:Digital Press , Scorpio [Digital Press , Scorpio]
Chapter Three: An Introduction to Loops Loops are for when you have to do a similar task multiple times. Say for example, you have to write the names of your ...
( Category:
Computers & Technology
August 19,2019 )
epub |eng | 2017-10-01 | Author:Dvorjak, Keith [Dvorjak, Keith]
Chapter 9 Error handling What are errors? Errors are basically unexpected conditions that may or may not halt the execution of a program during the runtime of a program. Errors ...
( Category:
Programming Languages
August 18,2019 )
epub |eng | | Author:Mauro Conti
2. smart: At each step of the attack sequence, the next node to tamper with is node s, where s maximizes S(s), . Intuitively, the oblivious adversary does not take ...
( Category:
Computers & Technology
August 18,2019 )
epub |eng | | Author:Sunil Cheruvu & Anil Kumar & Ned Smith & David M. Wheeler
In addition to thread execution priorities used to enforce time separation of threads, Zephyr assigns a thread privilege to each thread. There are only two privileges, supervisory and user. By ...
( Category:
Network Security
August 18,2019 )
epub |eng | 2019-08-05 | Author:Robert Wilson
THIRTEEN * * * * * * A RUINED MAN After the Jenny Lind tour ended, Barnum briefly but seriously considered moving the family to Philadelphia, where he owned a ...
( Category:
United States
August 18,2019 )
epub, mobi, pdf |eng | 2015-06-17 | Author:Excel Expert [Expert, Excel]
( Category:
Computers & Technology
August 17,2019 )
epub |eng | 2019-09-30 | Author:Susan Schneider [Schneider, Susan]
DITCHING YOUR SUBSTRATE? Modified patternism faces a second problem as well, one that challenges the very possibility that an individual could transfer to a different substrate, even with no cognitive ...
( Category:
Intelligence & Semantics
August 17,2019 )
epub |eng | 2019-08-06 | Author:DataTech Publishing [Publishing, DataTech]
( Category:
Computers & Technology
August 17,2019 )
epub |eng | 2019-04-30 | Author:Fabio Alessandro Locati
If you declared an entry for your public zone but not in the private one, the machines in the VPC will not be able to resolve that entry. After you ...
( Category:
Bioinformatics
August 17,2019 )
epub |eng | | Author:David Both
Let’s look at the so-called hidden files in your own home directory – those whose names begin with a period (.). These are user-specific configuration files that you can change ...
( Category:
Software Development
August 17,2019 )
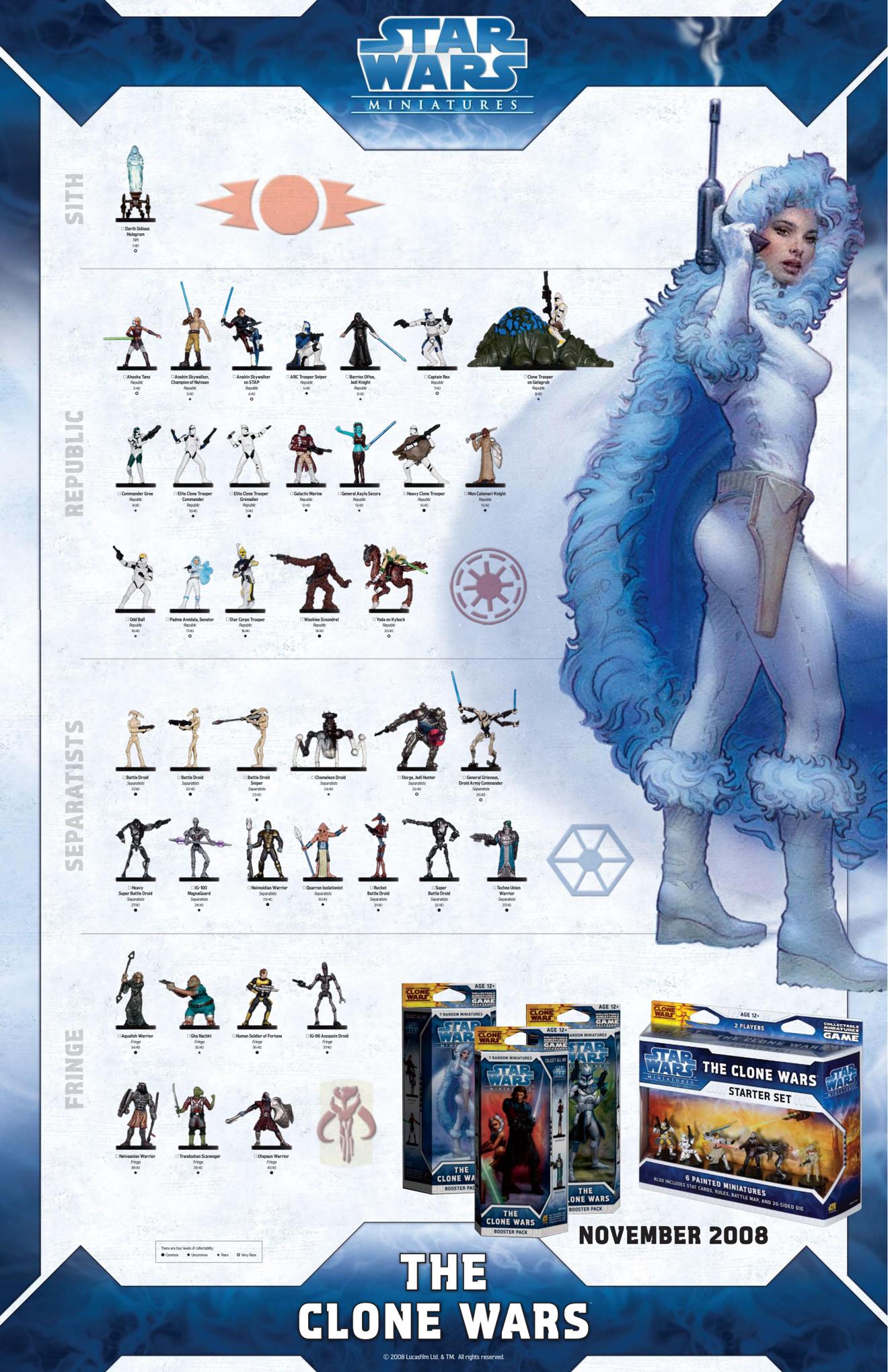
epub, pdf |fra | 0101-01-01 | Author:Unknown
But Ventress wasn't defenseless. As Anakin swung his lightsaber, she ducked and used the Force to push him backward, taking him by surprise. He smashed against the wall, dropping his ...
( Category:
Science Fiction
August 16,2019 )
epub |eng | 2018-06-18 | Author:Anna Chastain [Chastain, Anna]
Chapter 27 Holly Red comes over on Tuesday with a bag full of tacos and kicks Dean out. “I’m the worst dinner buddy ever,” I tell him after inhaling my ...
( Category:
Romantic Comedy
August 15,2019 )
epub |eng | 2015-06-29 | Author:Seroter, Richard & Brimble, Mark & Cooper, Johann & Dijkgraaf, Colin & Morar, Mahindra
Now, we can switch back to the General tab and assign an HTTP address for this endpoint. I've chosen an arbitrary port number and URI (http://localhost:4044/SiteRegistrationService/service.svc) to represent this endpoint: ...
( Category:
Computers & Technology
August 15,2019 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(28003)The Mikado Method by Ola Ellnestam Daniel Brolund(25294)
Hello! Python by Anthony Briggs(24339)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(23434)
Kotlin in Action by Dmitry Jemerov(22512)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(21976)
Dependency Injection in .NET by Mark Seemann(21848)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(20715)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(19523)
Grails in Action by Glen Smith Peter Ledbrook(18609)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17034)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15843)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(13690)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(11857)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11151)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10621)
Hit Refresh by Satya Nadella(9202)
The Kubernetes Operator Framework Book by Michael Dame(8570)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8408)
Robo-Advisor with Python by Aki Ranin(8361)